Identity, Guardrails, and Contextual Visibility: Real-World Lessons from the CxO Security Forum
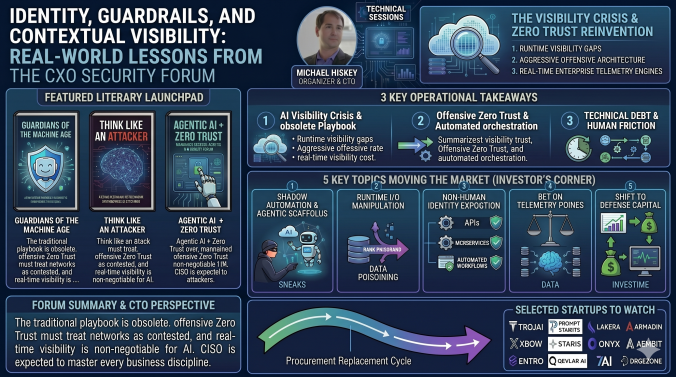
If you need a sign that the cybersecurity landscape has undergone a permanent phase shift, look no further than the structural changes reshaping our production environments. I recently had the privilege of sitting down with an incredible assembly of cybersecurity practitioners, engineering leaders, and market analysts at our latest CxO Security Forum held during the Gartner Security and Risk Summit at National Harbor. Thanks go out to Michael Hiskey for setting this up and Illumio for sponsoring the lunch.
Per our strict operational tradition, this gathering was conducted entirely under Chatham House Rules, meaning all CISO insights have been sanitized, and no security leaders are explicitly named or attributed to ensure a raw, unvarnished look at what’s actually happening on the front lines.
Beyond the intense architectural debates, the session doubled as an incredible literary launchpad: industry analyst Richard Stiennon was on hand signing his new book, advanced copies of Guardians of the Machine Age: Why AI Security Will Define the Future of Digital Defense, capturing all of the new AI companies that are out there. At the same time, zero-trust pioneer Dr. Chase Cunningham showcased his book, Think Like an Attacker: Why Security Graphs Are the Next Frontier of Threat Detection and Response. Finally, we had John Woodruff, who shared insights from his book Agentic AI + Zero Trust: A Guide for Business Leaders.
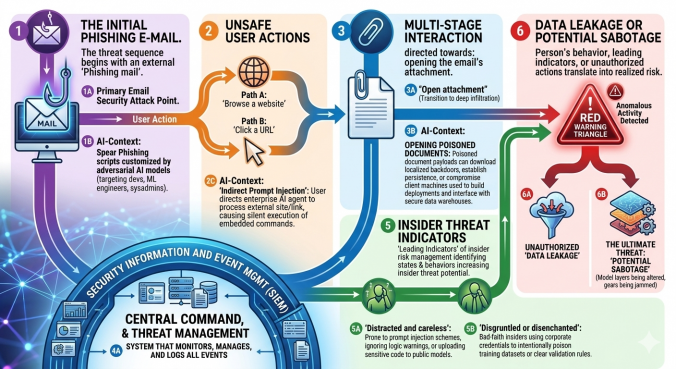
From my perspective as a former CISO and current CTO, the absolute biggest operational takeaway from the forum is that the traditional security playbook isn’t just aging; it’s completely obsolete. During our technical session, an attendee stressed that engineering teams are experiencing massive visibility gaps when it comes to understanding AI applications at runtime. One of the attendees noted that trying to secure machine learning pipelines using static database auditing or old-school perimeter boundary checks is an absolute non-starter.
Organizations are dynamically ingesting massive quantities of unstructured data at the execution layer. As another attendee pointed out, security teams must deploy dynamic, runtime data classification capabilities right at the execution level to intercept malicious prompt overrides and stop corporate data leakage before the model processes the query.
Zero Trust – CISO know it’s a journey and not a destination…
This visibility crisis ties directly back into how we design and execute a modern Zero Trust strategy. Too many organizations treat zero trust as a passive product check-box, but as an attendee rightly pointed out, true resilience requires an aggressive, offensive-minded architecture that assumes compromise from day one. I have spent a good number of years speaking to the importance of “choosing a framework” and “architecture” and this session provided even more affirmation that my pulpit is not for nought. It’s critical CISO’s have the business acumen to lead up the chain as well as the technical prowess to lead their teams in the right direction. Without the architectural vision the program is doomed to fail.
The discussion heavily focused on leveraging real-time enterprise telemetry to fuel centralized policy engines. One attendee broke down how these automated engines must function as the central brain of your architecture, constantly calculating risk and dynamically broker credentials across users, data assets, and machine-to-machine microservices. When you stop looking at your network as a safe zone and start treating your internal infrastructure as a contested space, you’re forced to build the explicit guardrails necessary to choke off lateral movement and minimize the blast radius.
CISO’s need degrees, certs, 100 years of experience, and luck…
It was mutually agreed that unlike the CFO, CIO, COO, etc the CISO is expected to know about every discipline across the organization. They need to have some understanding of finance, business process, back-end systems, front line workers, and all the tech as well. It’s an insane amount of burden on one individual. There was mixed feeling about how to delegate and train up our teams as well. Some Execs felt that ISC2 has not kept up with the times and the certs are not useful for their teams while others felt some were needed to set a baseline of knowledge.
We had one recent grad in the room who has a degree in computer science and cannot land a role in cybersecurity (In spite of our so called 3.5m open Cyber Security reqs) because he is a recent college grad. He mentioned every “entry level” job required 3-5 years’ experience and he was wondering how one gets this without being able to land a job in the first place. The CISO’s voiced their concerns with students coming out unprepared and lacking basic knowledge in how networks actually work. Seems to be one focus and that’s “I can use AI” which could mean they know how to generate a cool picture but not how to see what traffic is coming over a specific port.
Finally, the room got incredibly real about the human cost of technical debt. An attendee broke down how the intense winter weather gridlock and localized school closures completely stalled out critical development pipelines and engineering support systems. It proved a vital point: if your security stack is a fragile legacy blueprint, real-world disruptions will cause immediate operational burnout. Engineering teams cannot keep drowning in manual triage every time an unexpected external stressor hits the architecture. We can’t boil the ocean, but as security leaders, we have to engineer low-overhead, automated orchestration layers that maintain continuity when manual workflows break down.
As security leaders, we have to look at our organization like an engineering blueprint, we can’t boil the ocean, but we must implement low-overhead, automated orchestration layers that decouple core security policies from manual human dependencies, so operations remain fully operational when things go sideways.
🚀 Investor’s Corner: Hot Topics & PE/VC Guidance
The deep structural transformations discussed during the forum are sparking a massive, multi-year procurement replacement cycle across enterprise security stacks, creating prime entry points for private equity and venture capital firms backing early-stage peer innovators (Seed / Series A).
Hot Topics Moving the Market
- Shadow Automation & Agentic Scaffolds: Employees are actively bypassing corporate boundaries by wiring unauthorized AI agents directly into internal databases and sensitive corporate codebases to chase productivity shortcuts.
- Runtime Input/Output Manipulation: Adversaries are shifting away from traditional network exploits toward runtime attacks like data poisoning, prompt injections, and dynamic instruction overrides.
- The Non-Human Identity Explosion: The massive proliferation of microservices, automated workflows, and machine-to-machine APIs has turned API and non-human authentication into the primary attack vector for modern adversaries.
Early-Stage Peer Innovators to Track
- Input/Output LLM Proxies: TrojAI, Prompt Security, Lakera
- Automated Red Teaming & Attack Simulation: Armadin, XBOW, Staris
- Non-Human Identity Governance: Onyx, Aembit, Entro
- Autonomous Threat Investigation: Qevlar AI, 7AI, Dropzone
Strategic Recommendations for PE/VC Firms
- Bet on Telemetry-Driven Policy Engines: Steer clear of fragmented point solutions. The platforms winning the market are those that seamlessly feed rich, distributed infrastructure telemetry directly into centralized, automated policy engines.
- Shift Capital Allocation to Runtime Defense: Static code analyzers and standard perimeter defenses are losing their premium. Focus investments on agile startups building inline, real-time protection and contextual, execution-layer data classification frameworks.
At the end of the day, our forum made one reality crystal clear:
The era of delayed log analysis and perimeter-based security boundaries is officially dead. Navigating this current landscape requires a total commitment to an offensive zero-trust posture, one anchored by continuous authentication, automated policy orchestration, and real-time visibility at the exact point of runtime data execution. For both security leaders looking to protect their enterprise and investors looking to deploy capital, the strategy moving forward means discarding legacy architecture and implementing the agile, runtime guardrails necessary to actively defend data in a contested space.
💬 Let’s Talk in the Comments!
- How is your team tackling runtime visibility and data classification for incoming unstructured AI pipelines?
- How are you re-architecting your central policy engines to keep track of non-human identity sprawl and machine credentials you can’t manually audit?
- When severe external stressors or environmental disruptions crash into your technical debt, how are you effectively leveraging low-overhead automation to keep your baseline security orchestration live?
#CyberSecurity #CISO #AI #MachineLearning #InsiderRisk #TheSecurityCafe #ThreatModeling #cxosecurityforum #startups #privateequity #venturecapital #gartner #CIO #CTO #cloudsecurity #onprem
Stay caffeinated, stay secure.
Please reach out to me or Boston Meridian Partners via our webpage and LinkedIn below.
Boston Meridian LinkedIn Page <- Follow this company!
About the Author:
I am Shawn Anderson, CTO and 2x former CISO, currently leading technical strategy at Boston Meridian. We are a boutique investment bank specializing in M&A and capital raises ($20m+) for the Cyber and Infrastructure sectors. Let’s connect on LinkedIn to discuss where the market is moving next.